Index
Integration with Active Directory
There are three ways to integrate fluig Identity with Active Directory (AD):
- Integration for user synchronization and access with AD credentials via SmartSync.
- Integration for Single Sign On via Desktop SSO.
- Integration for access granting and revoking in AD, via administration on fluig Identity.
In the first two cases, we use support components to enable this integration. SmartSync is a desktop component built in .NET that allows configuring the connection between fluig Identity and Active Directory domains with which to perform the integration. In this configuration, the following connection data must be entered:
- AD server addresses.
- DN base.
- User with AD administrative permission for reading and writing.
- Admin user password.
- Connection token created by fluig Identity.
Due to these details, it is crucial that the customer chooses an employee that has know-how of the company's Active Directory infrastructure to provide this information.
In the case of Desktop SSO, it is a script that should be installed in IIS and displayed in such a way that fluig Identity can access it.
This script will be responsible for enabling Single Sign On (SSO) for fluig Identity. Provided that the user has entered their network credentials when logging on to Windows, no username or password will be required when they try to access fluig Identity or any application integrated with fluig Identity.
Architecture
Fluig Identity has a component called SmartSync, which acts as an agent between fluig Identity and the customer's Active Directory, and is responsible for:
- Running the initial import of users from AD.
- Allowing a fluig Identity user to use their AD credentials for authentication.
- Synchronizing the data between Active Directory and fluig Identity, including information on the existing users' accounts and new accounts to be created in AD.
It is important that SmartSync is always available so that it can provide synchronization and authentication with AD credentials. In case this component is offline, fluig Identity users have a contingency to continue accessing their applications, which consists in using their own credential (personal password), which is set as the user is enabled.
See below examples of some possible scenarios:
- One server with SmartSync installed, providing synchronization and authentication with AD credentials.
- This scenario comprises the integration between fluig Identity and Active Directory, including user synchronization and authentication using AD credentials.
- High availability not included.
Simple scenarios, no SSO and high availability.
- Two servers, each one with SmartSync installed, providing high availability for synchronization and authentication with AD credentials.
- In this scenario, there are two servers to synchronize users and authenticate with AD credentials. If either server goes offline, the other one keeps supporting user synchronization and authentication.
- There is no need for a Load Balancer because SmartSync has an active behavior consuming a line of requests provided by fluig Identity.
- Single Sign On is not available in this scenario.
Scenario providing high availability for synchronization and authentication with AD credentials, Single Sign On not included.
- One server with SmartSync and Desktop SSO installed, providing user synchronization and Single Sign On for fluig Identity using the AD credentials entered when logging on to Windows.
- In this scenario, SmartSync provides user synchronization and Desktop SSO provides Single Sign On. Provided that the user has properly entered their credentials to log on to Windows, they can access fluig Identity without having to enter their credentials again.
- This scenario does not offer high availability.
- If Desktop SSO is offline, users can authenticate into fluig Identity with their AD credentials.
- If SmartSync is off-line, users can access fluig Identity using the credentials entered when their account was enabled. This is a contingency credential.
Scenario in which there is user synchronization and Single Sign On to access fluig Identity, but no high availability
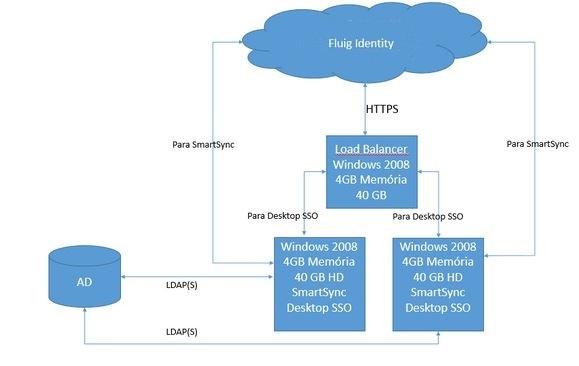
- Three servers, two of which have SmartSync and Desktop SSO installed, providing a high availability environment, and a third one working as Load Balancer.
- In this scenario, SmartSync provides user synchronization and Desktop SSO provides Single Sign On. Provided that the user has properly entered their credentials to log on to Windows, they can access fluig Identity without having to enter their credentials again.
- This scenario offers high availability.
- If Desktop SSO is offline, Load Balancer directs the request to the online server.
- If a SmartSync is offline, the other installation continues to provide the user synchronization service.
Scenario where there is user synchronization, Single Sign On, and high availability.
Requirements
It would be ideal to provide a high availability environment, with 2 computers dedicated to SmartSync and Desktop SSO, and a third one used for load balance, in the case of Desktop SSO.
The customer can also choose to use only 1 machine on which to install SmartSync and Desktop SSO, eliminating the redundant machine and Load Balancer.
See the Portability Matrix - fluig Identity for the required hardware and software for synchronization of users with AD, authentication with AD credentials and Single Sign On.
This server, or servers if the customer chooses high availability, needs to meet a few more requirements:
- Internet access, for connection to fluig Identity.
- Access to domain or domains to be configured on SmartSync.
- User with AD administrative privileges to synchronize and authenticate users and/or assigning and removing users in AD.
- The machine where to install SmartSync/Desktop SSO should not be the same as where the AD/domain controller is installed so as to prevent it from being exposed to the internet.
Attention
If Active Directory is directly integrated with fluig, that is, not via fluig Identity, make sure to disable this configuration before integrating AD in Identity. Otherwise, there may be access conflicts and invalid user errors on screen when using fluig.